A workplace violence threat assessment is a systematic evaluation of individuals, situations or conditions that could lead to violent acts in a work environment. It is not about predicting violence with certainty - it is about identifying warning signs early enough to intervene before a situation escalates. Workplace violence is the third leading cause of fatal occupational injuries in the United States, accounting for approximately 700 deaths and tens of thousands of non-fatal injuries each year. Every organization - regardless of size, industry or location - needs a process for assessing and managing threats.
This guide explains how to build and implement a workplace violence threat assessment program, including the types of workplace violence, how to form a threat assessment team, what warning signs to recognize and how to take action that protects employees while respecting legal and ethical boundaries.
Types of Workplace Violence
The National Institute for Occupational Safety and Health (NIOSH) classifies workplace violence into four categories. Understanding these categories is the first step in any threat assessment because each type involves different risk factors, warning signs and prevention strategies.
Free Download: 5 Safe Work Procedures
Choose from 112 professionally written SWPs. No credit card required.
Get Free SWPsType I: Criminal Intent
The perpetrator has no legitimate relationship to the workplace or its employees. The violence occurs during the commission of a crime, most commonly robbery. Late-night retail, convenience stores, gas stations and taxi services are at highest risk.
Type II: Customer or Client
The perpetrator is a customer, client, patient, student or other person receiving services from the organization. Healthcare workers, social service employees, teachers and customer-facing staff are most commonly affected. This is the most prevalent type of workplace violence.
Type III: Worker-on-Worker
The perpetrator is a current or former employee who targets coworkers, supervisors or managers. This type often involves an escalating pattern of behavior that is observable before the violent act occurs - making it the most amenable to threat assessment intervention.
Type IV: Personal Relationship
The perpetrator has a personal relationship with an employee (spouse, partner, family member, friend) and brings that conflict into the workplace. Domestic violence that follows a victim to work falls into this category.
A comprehensive threat assessment program must address all four types. For an overview of workplace violence prevention strategies, see our workplace violence prevention guide.
What Is a Threat Assessment?
A threat assessment is a fact-based process of evaluating a specific person's behaviors and circumstances to determine whether they pose a genuine risk of violence. It differs from profiling (which attempts to predict violence based on demographic characteristics) and from zero-tolerance policies (which treat all threatening statements the same regardless of context).
Effective threat assessment asks three fundamental questions:
- Is this person on a pathway toward violence? Are they taking steps that indicate planning, preparation or escalation?
- What is the person's intent and capability? Do they have the motive, means and opportunity to carry out violence?
- What can be done to manage the risk? What interventions - support, discipline, security measures, referrals - can reduce the likelihood of violence?
The goal is not to label someone as "dangerous" but to understand a situation well enough to manage it effectively.
Building a Threat Assessment Team
A multidisciplinary threat assessment team (TAT) is the engine of an effective program. No single person has the expertise to evaluate threats from every angle. The team brings together perspectives from multiple disciplines to make informed decisions.
Recommended Team Members
- Human Resources: Provides employee history, performance records, disciplinary history and knowledge of personnel policies
- Security: Assesses physical security measures, conducts investigations and coordinates with law enforcement when necessary
- Legal counsel: Advises on employment law, privacy, liability and the legal boundaries of interventions
- Management representative: Offers operational context about the workplace, the individuals involved and business considerations
- Mental health professional: Provides clinical perspective on behavior patterns, risk factors and appropriate referral resources (note: this person does not diagnose the subject - they advise the team)
- Safety/EHS representative: Connects the threat assessment process to the broader workplace safety program
For smaller organizations, the team may consist of just two or three people. The critical requirement is that the team has the authority to act and the access to information needed to make informed decisions.
Team Protocols
Establish clear protocols before a threat occurs:
- How are threats reported to the team?
- How quickly must the team convene after a report?
- What information does the team collect and from whom?
- How are decisions documented?
- What are the escalation thresholds for involving law enforcement?
- How is confidentiality maintained?
- How are outcomes monitored over time?
Recognizing Warning Signs
Most acts of workplace violence are preceded by observable warning signs. No single indicator predicts violence, but patterns of behavior - especially escalating patterns - should trigger a threat assessment.
Behavioral Warning Signs
- Increasingly angry or hostile outbursts
- Direct or veiled threats against coworkers or the organization
- Fascination with workplace violence incidents or weapons
- Statements indicating hopelessness, desperation or a desire for revenge
- Significant changes in behavior, appearance or performance
- Social isolation or withdrawal from colleagues
- Paranoid thinking or expressions of persecution
- Blaming others for personal or professional problems
- Excessive absenteeism or tardiness without explanation
- Substance abuse or signs of intoxication at work
Situational Risk Factors
- Recent termination, layoff or disciplinary action
- Ongoing workplace conflict or harassment
- Domestic violence that may extend to the workplace
- Financial stress, legal problems or custody disputes
- Access to weapons
- History of violent behavior
- Loss of a relationship or significant life event
- Perception that all other options have been exhausted
It is important to emphasize that exhibiting one or even several warning signs does not make a person violent. The purpose of identifying warning signs is to trigger a careful assessment - not to make accusations or take punitive action prematurely.
Conducting a Threat Assessment
When a potential threat is reported to the team, follow a structured assessment process.
Step 1: Gather Information
Collect facts from multiple sources:
- The person who reported the concern
- Witnesses to the behavior or statements
- The subject's supervisor and coworkers (approached carefully to avoid stigmatization)
- HR records (performance reviews, disciplinary actions, complaints)
- Security records (access logs, prior incidents)
- Public records (where legally appropriate and relevant)
Focus on observable behaviors and specific statements - not rumors, personality assessments or diagnoses.
Step 2: Evaluate the Threat Level
Assess the information against established risk factors. Many organizations use a tiered classification:
- Low risk: Behavior is concerning but does not indicate a pathway toward violence. The person may be stressed or frustrated but has no history of escalation and no indicators of planning or capability
- Medium risk: Behavior shows patterns consistent with escalation. The person may have made indirect threats, exhibited increasing hostility or demonstrated fixation on a grievance. Intervention is warranted
- High risk: Behavior indicates a clear and present danger. The person has made direct threats, taken preparatory steps (acquiring weapons, conducting surveillance, giving away possessions) or demonstrated an intent to harm
Step 3: Develop an Action Plan
Based on the risk level, develop a tailored response:
Low Risk Responses
- Monitor the situation through normal supervisory channels
- Offer employee assistance program (EAP) referrals
- Address underlying workplace issues (conflict, workload, management practices)
- Document the assessment and check back at defined intervals
Medium Risk Responses
- Direct supervisory intervention addressing specific behaviors
- Formal referral to EAP or mental health resources
- Increased monitoring and documentation
- Review of physical security measures
- Consider temporary reassignment or schedule modification
- Consult with legal counsel on appropriate employment actions
High Risk Responses
- Immediately involve law enforcement if a credible threat of imminent harm exists
- Remove the subject from the workplace (administrative leave, separation)
- Implement protective measures for potential targets (escorts, schedule changes, address confidentiality)
- Increase security presence and access controls
- Notify potential targets and provide safety planning assistance
- Coordinate with law enforcement for ongoing threat management
Step 4: Implement and Monitor
Execute the action plan and monitor outcomes. Threat management is not a one-time event - it is an ongoing process. Reassess at regular intervals and adjust the plan as circumstances change. Document every step.
Documenting Threat Assessments
Thorough documentation is essential for legal protection, regulatory compliance and continuity if team members change. Document:
- Initial report details (who reported, when, what was observed)
- Information gathered during the investigation
- Team meeting dates, attendees and decisions
- Risk level classification and rationale
- Action plan details and responsible parties
- Follow-up actions and reassessment findings
- Final disposition and case closure rationale
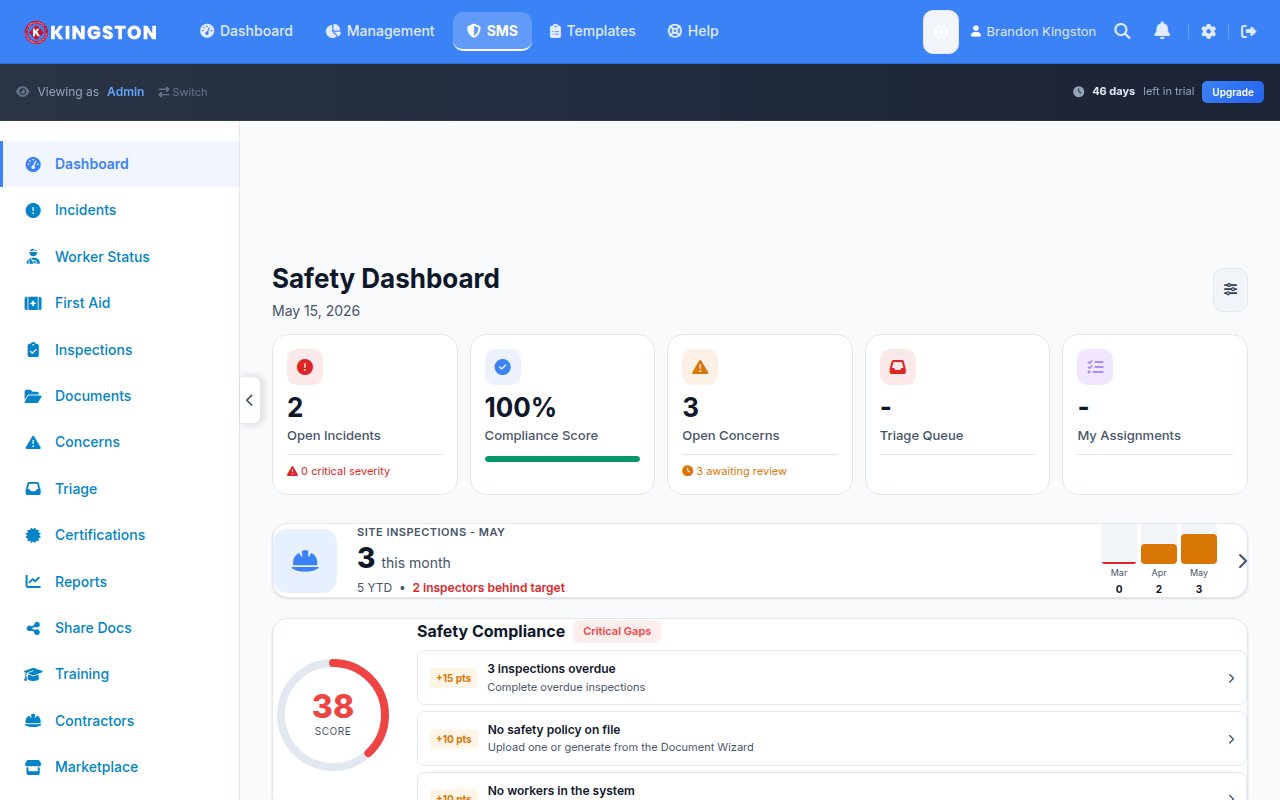
Maintain these records securely with access restricted to team members and authorized personnel. A digital incident reporting system provides the structure, security and retrievability that threat assessment documentation demands.
Legal Considerations
Threat assessments operate at the intersection of workplace safety, employment law and individual rights. Key legal considerations include:
- Duty of care: Employers have a legal obligation to provide a safe workplace. Failure to act on known warning signs can result in negligence liability
- Privacy: Balance the need for information with employee privacy rights. Consult legal counsel before accessing personal information
- Disability law: Mental health conditions may be protected under the ADA. Focus assessments on behavior, not diagnosis
- Defamation: Protect the subject's reputation by limiting information sharing to those with a legitimate need to know
- Retaliation: Ensure that reporting concerns is protected and that no adverse action is taken against reporters
Prevention Beyond Assessment
Threat assessment is a reactive tool - it responds to identified concerns. A complete workplace violence prevention program also includes proactive measures:
- Written workplace violence prevention policy
- Employee training on recognizing and reporting warning signs
- Reporting mechanisms that are accessible, confidential and free from retaliation
- Physical security measures (access control, surveillance, panic alarms)
- Employee support programs (EAP, conflict resolution, stress management)
- Regular workplace violence risk assessments of facilities and operations
- Post-incident response planning and trauma support
Build a Threat Assessment Program That Protects Your People
Workplace violence threat assessment is not about fear - it is about preparation. By establishing a trained team, creating clear protocols and acting on warning signs with a structured process, you give your organization the best possible chance of preventing violence before it occurs.
Make Safety Easy provides the incident reporting, documentation management and communication tools that support every phase of a workplace violence prevention program. Book a demo to see how the platform works, or explore our pricing to get started today.